Your phone dings. The message is dire. You’ve suspected the worst. And the worst has happened: An account on your network – maybe even your own – has been compromised.
The good news is a breach can be isolated and managed, especially if you’ve taken proper preventative measures. The fight to mitigate risk begins with a solid data security plan but continues every day. In the unfortunate and problematic event that you are compromised, use the steps below to help guide what you and your team should do immediately.
In the blink of an eye, millions of dollars in data, productivity, intellectual property, and more can be snatched away. In 2021, cybercrime cost businesses $6 trillion, making it the world’s third-largest economy on its own. Additionally, Cybersecurity Ventures expects global cybercrime costs to grow by 15% per year over the next five years, reaching an estimated $10.5 trillion by 2025.
Understanding the Threats
But first, how do they even get in?
Those looking to enter your system will take just about any chance they get to gain access. We can’t list every single new form of software every hacker is utilizing but here are a few key types of threats you should be aware of:
(Click titles for more info on each section)
- Malware & Ransomware Campaigns: Malware is software designed to wreak havoc on a computer, server, client, or even entire networks. Ransomware, on the other hand, is a specific type of malware that infects and restricts access to a computer until a ransom is paid. Ransomware is typically delivered through phishing emails (below) and exploits unpatched vulnerabilities in software (also below).
- Email Phishing Campaigns: A digital outlaw sends someone on your team an email containing a link or dangerous file which deploys their malware after it’s clicked by the recipient. Historically speaking, hackers have used generic “shotgun” strategies to deploy malware, through recent ransomware campaigns have become more targeted and sophisticated as optimal victims are identified.
- Remote Desktop Protocol (RDP) Vulnerabilities: RDP is a proprietary network protocol that allows individuals to control a computer and its contents (data, etc) via the internet. Cybercriminals have used both brute-force methods like trial-and-error to obtain user credentials and additionally utilize credentials purchased on dark web marketplaces to gain unauthorized RDP access to victim systems.
- Software Attacks via Unpatched Vulnerabilities: Savvy criminals can also take advantage of security weaknesses in widely used software programs your small business utilizes to gain control and deploy ransomware on your system.
{{cta(‘3ab4c43a-fe26-48c1-8963-828a9ae1d1b1’)}}
What To Do When You Are Compromised
Whether or not it’s your job to understand the specifics of how they got in or not, once your account is compromised, every second counts. Dragging your feet in the hopes of the problem being naturally contained is, quite honestly, dangerous behavior.
The first step to fixing any problem is admitting you have one, so here are the five things you must do when you’ve discovered that an account is compromised:
1. Contact Your IT Department Immediately
There’s no better alternative than having a dedicated team that has experienced these situations first-hand. Even if you’re simply wary of an odd occurrence on the network or notice something specifically suspicious, contacting your IT team immediately can help prevent further security issues – they’ll know what the most immediate next steps for the network are for your situation.
2. Change Your Password To Something Impossible To Guess
Keeping in mind that 23 million people continue to think “12345” is a solid password, we wanted to share a few thoughts on good password hygiene. Never, ever, ever share your password with someone unless you absolutely must – and even then, never share the password virtually. If you suspect that someone knows your password (or it has been compromised), change it immediately. Changing your password is an easy way to make sure no one else has unauthorized access to your account. When choosing a new password, remember these items:
- Don’t reuse passwords
This makes it easier for someone to break into multiple sites that use the same credentials. Think of topics beyond your first pet’s name or the street you grew up on by including complex phrases and sets of numbers. - Add some complexity
Speaking of complexity, make sure your password is at least 8 characters and uses lower case letters, upper case letters, numbers, and a special character or two for good measure. Even adding spaces between words helps. - Use a password manager
Password managers are a great tool to utilize in helping keep track of all of your passwords. They use a single password to store all your passwords in an encrypted file.
Further Reading: Four Practical Password Tips You Can Actually Follow (goptg.com)
3. Turn On Two- Or Multifactor Authentication
Microsoft isn’t shy with their reporting from 2020: 99.9% of all compromised accounts were not using the multifactor authentication tools available. Two-factor (2FA) and multifactor authentication (MFA) isn’t just important, it is literally as useful as using sanitizer after someone else coughs into your hands right before you eat dinner.
Okay, that may be a stretch of an analogy, but the point is not using some form of 2FA or MFA is reckless. Not only do two-factor and multifactor authentication solutions better help prevent theft and unauthorized access, but they also afford your team a higher degree of confidence that only your team is seeing your sensitive and confidential data.
Further reading: Making MFA More Convenient for your Business (goptg.com)
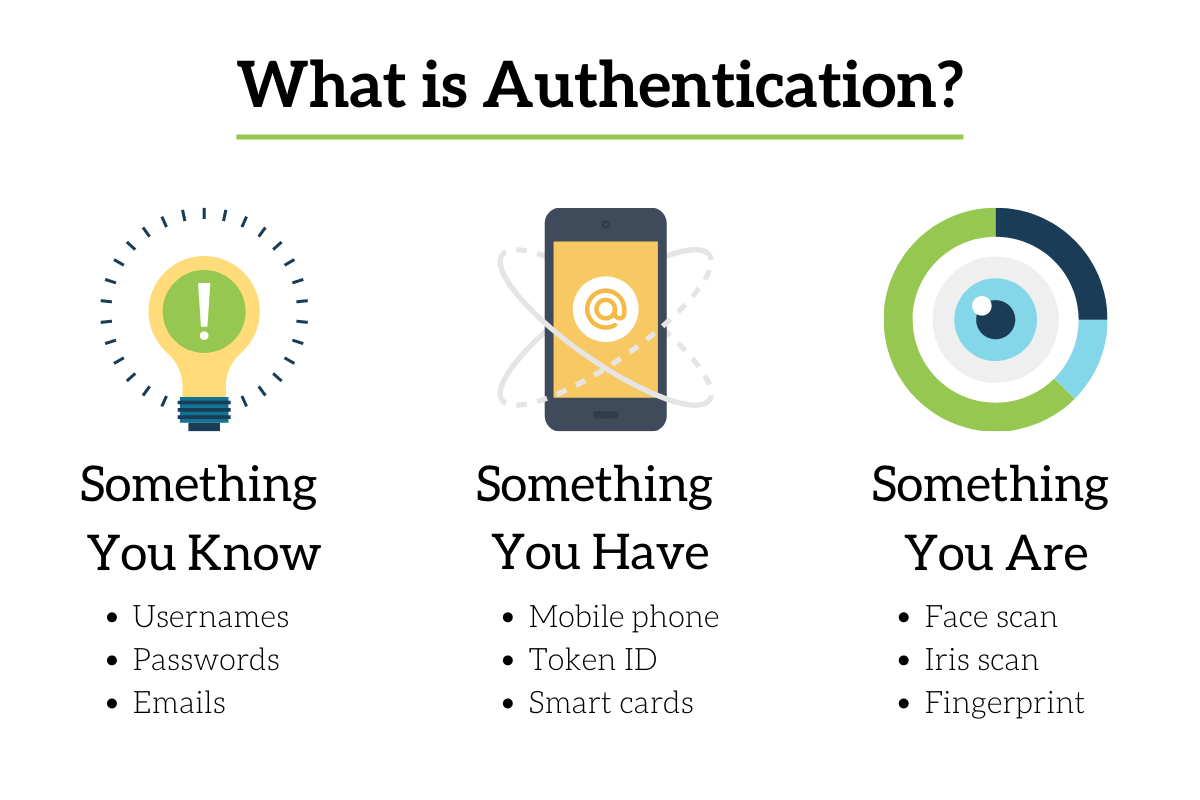
To beef up your security, your multifactor authentication should include at least two different authentication items.
Every organization is unique and should choose items from the list that fit the software, and needs, of their day-to-day. Duo, Google, and Microsoft all have applications that leverage MFA your business can use for free.
4. Check For Any Recently Created Mail Flow Rules
As cybercriminals skulk around your network undetected, they often spend time constructing trap doors that ensure the greatest amount of chaos when put into action. For instance, when someone compromises an account, they will often create email rules that make it significantly easier for them to cover their tracks, get copies of all your emails, and send out malicious links to others in your organization.
If you’ve been, or feel you’ve been, compromised, be on the lookout for rules like these appearing in your email:
- Forward a copy of every email to an external address.
- Automatically move emails with a certain keyword to the deleted items.
- Set up an automatic reply message with a bad link to anyone that emails you.
If you don’t know how to check your email rules, we found this article to be particularly helpful!
5. Review Your Recently Sent/Deleted Emails
Continue on your journey through your email by diving into both your sent and deleted folders to see what the attacker might have sent from your account. If there has been a significant break-in, you may have to engage with your IT department to review the messages that were deleted as well.
While there are nearly an infinite number of ways criminals can exploit your accounts, many have used compromised accounts to send emails asking clients to pay a bill to a different reception account or to change direct deposit information. If you find messages that fit those criteria, or anything else suspicious, you should follow up with the recipient to let them know what is happening and prevent additional problems.
In the end, while it may seem like a lot of work to be done to prevent cybercriminals from gaining access to your accounts, there’s even more work to be done if you are compromised. But being compromised doesn’t mean your world is over, it just means you better get rolling on some solutions.
About PTG
Palmetto Technology Group (PTG) is an award-winning IT support and managed service provider headquartered in Greenville, South Carolina. We believe in delivering phenomenal IT experiences by people you’ll love.
As a trusted partner, our goal is to help business owners lower their risk, secure their data, and promote productive employees. To learn more, book a meeting with one of our solutions specialists here.
{{ include_custom_fonts({“ProximaNW01Reg”:[“Regular”]}) }}